Unlocking the complexities of California's security deposit law is your key to a hassle-free renting…
Data Security in Therapy: Keeping Client Information Safe in the Digital Age – Guest Post
Confidentiality forms the foundation of the therapist-client relationship. As mental health services increasingly embrace digital technologies, safeguarding sensitive client data has become both a legal obligation and an ethical imperative.
In today’s era of escalating cyber threats, a single data breach can shatter hard-earned trust and disrupt the therapeutic process. This comprehensive guide explores the multifaceted challenges of data security faced by therapy practitioners.
The Sanctity of the Therapist-Client Relationship
Privacy and confidentiality are the bedrock of the therapist-client relationship, enabling the open and honest communication essential for effective therapy. The oath of Hippocrates, the foundational ethical guide for medical professionals, emphasizes the sacred duty of safeguarding patient confidentiality.
In the digital era where sensitive personal information is increasingly stored and shared electronically via EHR systems and practice management software, upholding this principle is critical yet challenging for mental health practitioners. A data breach compromising confidential client records can shatter hard-earned trust, impede therapeutic progress, and potentially cause immense psychological harm.
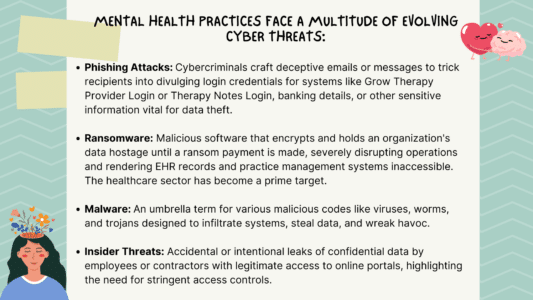
A Growing Danger: Current Threats to Therapy Data
Unfortunately, real-world data breach incidents in the therapy domain are on the rise. In December 2022, SalusCare, a prominent behavioral healthcare provider in Florida, experienced a devastating cyberattack resulting in the theft of patient records containing highly sensitive mental health treatment data.
Strengthening Digital Defenses: Best Practices
Robust cybersecurity is now a necessity, not an option, to protect client data integrity. Data encryption using strong algorithms like AES with 256-bit key lengths as recommended by HIPAA compliance standards is the foundational layer. However, a multi-pronged approach is required:
- Secure Electronic Health Records (EHRs): Deploying EHR solution with comprehensive security features like access controls, audit trails to monitor activity, and encrypted data transmission protocols when sharing records.
- Encrypted Communication Channels: Using end-to-end encrypted platforms and apps approved for HIPAA compliance like Signal, Spruce, and Cyphr for video sessions, messaging, and file transfers between therapists and clients.
- Secure Data Storage and Backup: Utilizing encrypted cloud storage services that meet regulatory requirements for healthcare practice management software, or on-premises storage solutions with robust access controls and redundant encrypted backups, helps prevent data loss.
- Network Security: Implementing firewalls, intrusion detection/prevention systems, VPNs for remote access, and routine vulnerability scanning to protect the practice’s IT infrastructure hosting EHR and therapy management solutions.
Navigating the Regulatory Landscape
Compliance with data privacy and security regulations is not just a best practice but a legal obligation. The HIPAA Privacy and Security Rules set forth by the U.S. Department of Health and Human Services establish national standards for safeguarding protected health information (PHI) encompassing medical and mental health records in EHR software and practice EHR systems.
Therapy practices, as covered entities, must adhere to HIPAA’s stringent requirements, including designating data privacy personnel, conducting risk assessments, maintaining audit logs, and implementing appropriate administrative, physical, and technical safeguards.
While HIPAA forms the federal baseline, some states like California, Massachusetts and Texas have enacted more stringent data protection laws that practices must additionally comply with if operating in those jurisdictions.
For therapists serving clients internationally, understanding data privacy regimes like the European Union’s General Data Protection Regulation (GDPR) that govern cross-border transfer and handling of personal data is imperative.
Fostering a Culture of Security Awareness
Even the strongest technological defenses can falter due to human error or lack of vigilance. A recent report reveals that a staggering 82% of data breaches involve human error. Therefore, it is vital to cultivate an organization-wide culture of security awareness through comprehensive training and ongoing education for staff handling EHR data and practice management tools.
It is crucial that all staff, from therapists to administrators, who interact with client data understand data handling protocols, recognize cybersecurity best practices such as identifying phishing attempts and managing passwords securely, and are aware of the serious consequences of negligence. Appointing a designated data privacy officer and conducting annual risk assessments can help identify vulnerabilities.
Crucially, open communication channels must foster an environment where employees feel empowered to report potential lapses or concerns without fear of reprisal. Prompt policy updates and simulated breach response drills should reinforce a security-first mindset throughout the organization’s EHR and practice management operations.
Technological Allies: Tools for Enhancing Data Security
While unwavering human diligence forms the frontline, intelligent deployment of specialized security tools and solutions can significantly bolster a practice’s cyber defenses for EHR platforms and therapy management systems:
- Automated Threat Detection: Leveraging artificial intelligence and machine learning models trained to detect anomalous patterns indicative of cyber threats like malware injection or unauthorized data exfiltration from EHR databases.
- Secure Communication Platforms: Embracing secure, encrypted platforms purposely designed for HIPAA-compliant communication between providers and patients. Leading examples include Signal for encrypted messaging and video calls, Cyphr for secure messaging and file sharing, and Spruce for HIPAA-compliant video conferencing to safeguard virtual therapy sessions.
- Identity and Access Management (IAM): Enterprise-grade IAM solutions, such as Okta, Ping Identity, and Microsoft Azure Active Directory, implement robust access controls and authentication protocols, including single sign-on and multi-factor authentication, to protect sensitive EHR systems and practice management portals.
The Road Ahead: Future Directions in Data Security
As digital technologies continually reshape mental healthcare delivery models through EHR solutions and practice management tools, data security strategies must also evolve and innovate. The COVID-19 pandemic accelerated the widespread adoption of telehealth and virtual therapy sessions, which are hosted on secure video platforms. However, this rapid transition has also expanded the cyber threat landscape as more client data traverses the internet.
On the cutting edge, decentralized technologies like blockchain hold immense potential for securely storing and sharing sensitive healthcare data from EHR systems without centralized vulnerabilities. However, advances in quantum computing pose an existential risk to current encryption standards that protect records. The use of genomic data for personalized therapies introduces new frontiers in data privacy challenges for EHR software developers.
Ongoing research by academia and industry, alongside interdisciplinary collaboration between clinicians, technologists, and regulatory bodies, will shape future data security paradigms for the mental health sector. Developing EHR platforms and therapy management tools with security in mind, while empowering clients as stakeholders in data governance, will be crucial for staying ahead of ever-evolving cyber threats.
Frequently Asked Questions (FAQs)
1. How can small therapy practices afford robust data security measures?
Prioritizing data security is crucial for practices of all sizes. Free and low-cost solutions like open-source encryption tools, secure messaging apps, and cloud storage services can provide a solid foundation. Additionally, investing in staff training and fostering a culture of security awareness can yield significant returns in terms of risk mitigation.
2. What immediate steps should a therapist take if they suspect a data breach?
In the event of a suspected data breach, immediate action is crucial. First, secure and isolate any compromised systems to prevent further damage. Next, consult legal counsel to understand your obligations under HIPAA and state laws. Finally, promptly notify affected clients and relevant authorities, while also implementing measures to mitigate the impact and prevent future occurrences.
3. How often should data security protocols be updated in a therapy practice?
There is no one-size-fits-all answer, as the frequency of security updates depends on various factors, including the practice’s size, technological infrastructure, and evolving cyber threats. As a general guideline, conducting comprehensive security assessments and policy reviews at least annually is recommended. Additionally, protocols should be updated promptly in response to any major security incidents, regulatory changes, or the adoption of new technologies.
Prioritizing Client Trust
In the digital age, safeguarding client data is not just a legal obligation, but a moral imperative for mental health professionals. By embracing best practices, leveraging technological solutions, and fostering a culture of security awareness, therapy practices can fortify their defenses against cyber threats and maintain the sacred trust of their clients.
Prioritize data security today to ensure the confidentiality and integrity of your client relationships for years to come.
